Microsoft Lync Server 2010 came in to UC domain while ago and it’s here to stay. Lync Server platform is far better than it’s predecessor Office Communicator 2007\R2 which including interoperability with various IPPBX platforms and VOIP Gateways.
One of the great features that came up with Lync Server 2010 is the SBA (Survivable Branch Appliance) and SBS (Survivable Branch Server) which add the surviveability to small branch offices when the connectivity to the central server is offline. I will cover this component in different post.
and the licensing changes introduced with the new platform makes it more affordable for the SMB market and given the ability to compete with high end IPPBX s such as CISCO Call Manager and AVAYA Platforms.
This article describe how to deploy Microsoft lync Server 2010 from the scratch to a successful client log in. Let’s devide the whole deployment process in to 3 steps.
1. AD\Domain infrastructure preparation
2. Applications Server preparation
3. Deployment of Lync Server 2010 software
Let’s start with Step 1
AD\Domain infrastructure preparation
Before getting in to deployment, it’s impotent to check the health of all the domain controllers within the domain. It’s a must that Domain controllers replication are healthy and no errors in the process. If there’s any problem found, those problems need to be fixed before the deployment. Also the domain and forest functional levels of the domain controller should be at least Server 2003.
Another important part of this deployment is the Enterprise Root Certification Authority Server. This CA will provide certificates to Lync Server role services as all communication between server roles are encrypted.
check http://technet.microsoft.com/en-us/library/gg412986.aspx for detailed information regarding the infrastructure requirement.
when ready, create 4 new DNS A records as shown below against the IP address of the Lync Server Front End Server.
- sip.uctest.com
- dialin.uctest.com
- meet.uctest.com

Create a DNS SRV record as below to get clients to automatically discover the Lync Server
- _sipinternaltls._tcp.uctest.com:5061

As a Best Practice, it’s always good to use a Service Account to deploy the application. In this scenario, i’ll use a user account called “SvcLync”. It’s a must that this user account has to be in Domain Admin, Schema Admin and Enterprise Admin security groups.
Now the infrastructure is ready for Lync Server. Let’s Prepare the Application server for Lync Server 2010 Standard Edition Front End Server
Application Server Preparation
The Server OS that i used for this deployment is Windows Server 2008 R2 X64 with SP1. Keep in mind that Lync Server only support x64 Operating Systems only. It’s recommended the server to be patched to the latest patch that available along side with the Service Pack. You can find the detailed hardware requirement in http://technet.microsoft.com/en-us/library/gg398835.aspx.
If it’s a production set-up, it’s recommended to use the Lync Server 2010 Planning tool to plan the complete deployment. you can download the planning tool from http://www.microsoft.com/en-au/download/details.aspx?id=19711
Login to the server using the Service Account and install Prerequisites to the Front End server. Run the below command in Powershell as the Administrator.
Import-Module ServerManager
Add-WindowsFeature NET-Framework,RSAT-ADDS,Telnet-Client,Web-Server,Web-Static-Content,Web-Default-Doc,Web-Http-Errors,Web-Http-Redirect,Web-Asp-Net,Web-Net-Ext,Web-ISAPI-Ext,Web-ISAPI-Filter,Web-Http-Logging,Web-Log-Libraries,Web-Http-Tracing,Web-Windows-Auth,Web-Client-Auth,Web-Filtering,Web-Stat-Compression,Web-Mgmt-Console,Web-Scripting-Tools -Restart
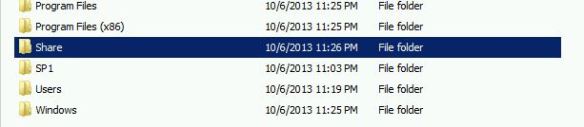
Create a folder called “Share” and assign read and write permission for “Everyone”
Restart the server when prompted. After the server comes up again, Add the service account to the local administrators group in Front End Server. Now we are good to go with Lync Server deployment
Deployment of Lync Server 2010 Software
Now load the Lync Server media and run the installation file. Select to Install it prompted to install VC++.

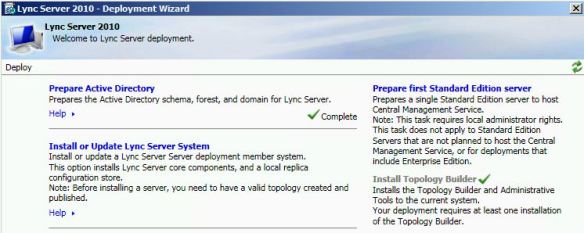
Open up the Deployment Wizard and let’s start with the Active Directory Preparation step. At this point, it’s very important to verify that the AD replication is healthy. Else some components of this step will fail

select to prepare the Active Directory

Schema Prep has completed Successfully.

notice the Green check mark next to the Schema Preparation Step indicating that the step completed successfully

Now Prepare the Forest. Select the Prepare Current Forest step

At this point you need to specify what forest that need to be prepared. This step has to run for all the domains that available if those domains are used in Lync Server platform. in this scenario, I’m selecting local domain as there’s no other domain available in this set-up

Proceed with the Preparation and finish the step.

Both the Schema preparation and Forest Preparation are successfully completed. Give it some time replicate the attributes across the forest

Now to prepare the Domain. Select the Domain preparation step

Completion of this step is depending on the AD replication process. If all is well, this step will complete successfully

The AD Preparation is successfully completed. All checks are green

Now go back and install the Topology Builder. Unlike OCS, Topology builder is the centralized tool that used in Lync server deployment to specify server roles and FQDNS for the rest of the deployment.
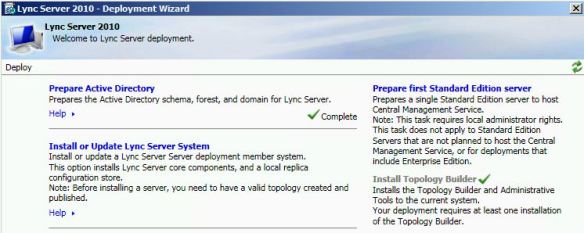
Now to deploy the 1st Standard Edition Server. This step is important as the 1st Standard Edition server keeps the Central Management Data store. there can be many Front End servers but the CMS will always be in 1st Standard Edition FE server

Proceed with the installation and complete the step. All checks are green and good to go ahead

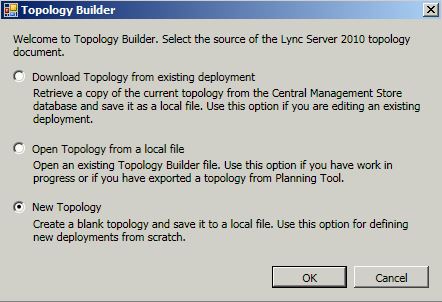
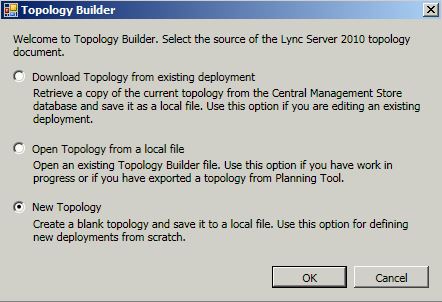
Now, let’s go back to the Topology. Open up the topology builder and select to deploy a New Topology
Save the topology and specify the primary SIP domain. This is the Primary SIP domain. there can be many additional SIP domain and can be added any time even after the deployment

This is where to configure all the additional SIP Domains that are available. I’m leaving as blank as there’s no additional SIP domains to configure

Now to define the Front End server pool.

Define the FQDN of the Front End server and select to deploy the Standard Edition Server. Make sure that you get the above FQDN right. If you get this one wrong, you’ll be end up cleaning AD objects using ADSIEDIT.

Now configure the services that goes in to the Front End Server. I’m selecting all services for this deployment

No select what are the server roles that can be collocated in to same box. A\V conferencing server will get collocated by default in to Standard Edition FE server but it can be deployed i a separate box in Enterprise Edition. mediation Server can be scattered or collocated regardless of the Lync Server version

Select what are the other server roles that are going to be deployed. I’m not going to deploy any other roles and leaving it black. Will cover deployment of these roles in up coming posts

Now define the File Share store. This is the share folder that I created while ago. this share folder will host Address Book files, UC Phone Updates and meeting contents.

Configure the External Web Services URL. There have to be an A record created in Public DNS for this host name and This URL need to be published in TMG and reverse proxy in to Front End server.

Complete the rest of the steps. go back to the Standard Edition server in the topology and edit properties. specify the CMS Server and the admin URL

All looks good. now publish the topology

Topology published successfully. now to install the services in Front End server. to do that, run the deployment wizard again and select “Add remove Lync Server Components”

Step 1, Install the Local configuration Store. before getting in to this, the service account need to be added in to CSAdministrator and RTCUniversalServerAdmins security groups. if not, this step will be likely to fail. once ready, run the step. select to retrieve the CMS directly.

Local Configuration Store deployment successfully completed. all checks green

Now to Step 2. Setup or Remove Lync Server Components. Run the step and reboot the server when prompted.

Run the step after rebooting the server. The step will complete successfully.

Step is completed and checked green

Step 3. request and install certificate. select the default certificate and request.

Request the certificate immediately from the internal Root CA

Select the root CA and specify a friendly name for the certificate. select the certificate as Private key exportable

Select the SIP domains that included in to this certificate. make sure that the check box for relevant domains are checked

Once requested, assign the certificate in to Front End services. All good and green.

Step 4. Start the services. Select to start the service and go in to Windows servers and verify that all the Lync Server services are started

The deployment is completed. now to test a user login. enable a user for Lync Server

Login to the client using the user credentials. Clint signed in successfully.